Reading through the well-written CCDE Study Guide book by Marwan Al-shawi, came to a section about having BGP as the Enterprise Core Routing Protocol and its possible Design models.
To make it a little bit brighter to myself, I’m gonna explain them in a different way with different diagrams and matrix based on my own design experience with these models.
Disclaimer: Please have in mind that the number of routers drawn, doesn’t reflect the reality of the design, and is just been this way for the sake of simplicity; obviously there would be redundant routers in real World, and also the Core could span different PoPs.
Besides, the bigger border routers could reflect two separate ones, one on Core, and one on Branch side.
Design Model 1
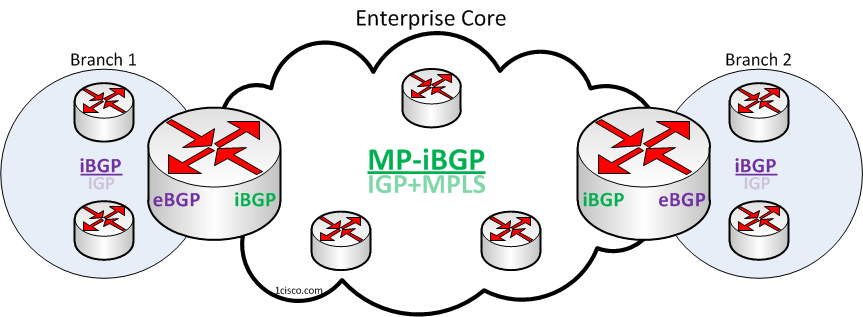
This model is suitable when least Administrative Domain Control is required; though it still overcomes an end-to-end IGP design, providing better management between remote campuses.
Core IGP is mainly used to provide Next-hop reachability for iBGP speakers. Please note that this is applicable to all models where iBGP is used in the Core.
The downside to this design is moderate operation complexity; which could arise i.e. by IGP-into-BGP Redistribution and iBGP full-mesh/RR/Confederation management in the Core. Continue reading “Enterprise Core Routing Design Models with BGP”