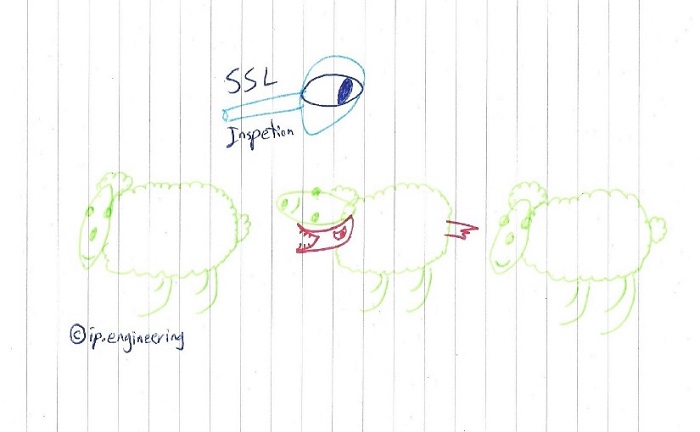
Having SSL Inspection has been always a matter of IT and Organisation fight.
In an architecture project, the only objection to my design was SSL Inspection and I had to bring some convincing reasons for that.
First of all, without SSL Inspection, basically there is zero visibility into what’s happening inside an encrypted traffic like HTTPS, SMTPS, POP3S, etc. Just imagine an attacker popping a machine, tunneling command and control via a HTTPS tunnel. Or an unfortunate employee, exposing confidential data by uploading them to some random cloud service… 0 visibility!
Second business driver I can think of is related to Data Loss Prevention; If a breach is detected tomorrow, there’s hardly any ways to detect what has been lost.
Benefits aside, a noteworthy drawback to SSL Inspection would be administrative overhead; you should distribute the CA cert to all nodes. That being said, in case of a Directory environment like Microsoft AD, it’s not a big deal, although Linux machines or some browsers need special configuration; beside, some web applications have to be excluded from inspection, mainly the ones utilizing Java.
Not really a drawback, but the administrators should be liable and trusted as they can easily intercept the traffic, unencrypted. This not only applies to the Proxy admins, but to a Mail admin, System admin, etc; which makes it an HR matter.
Note that any product which does MITM has the opportunity to expose data, and so its admins.
Here, you have to see the tradeoff; I believe the gained visibility worths it!
Sometimes CxOs might say that SSL is sacred! Yes, it is, but they have to decide how sacred they want SSL to be versus how interested they are in what information might be leaving the environment without authorization; or how much malware command and control (C&C) they might want quietly going out via SSL without being torn open for inspection.
Note that you have to design a way that all egress web traffic (both users and servers) must be enforced to go through the proxy, otherwise the whole proxy plan is pointless. Besides, you have to follow some practices:
- Know the business and business processes and demands. Every sector has its own limitations or requirements where might be against SSL inspection.
- Plan some whitelisting policies to disable inspection in specific cases where needed.
- Know your traffic and the percentage of encrypted requests.
- Make sure that your appliance supports the amount of traffic; SSL Inspection means decrypting the connection, inspecting it and then re-encrypting it.
P.S. Yes, my drawing skills are awful! ?