This post is my snippet of Wikipedia article about ISMS.
The governing principle behind an ISMS is that an organization should design, implement and maintain a coherent set of policies, processes and systems to manage risks to its information assets, thus ensuring acceptable levels of information security risk.
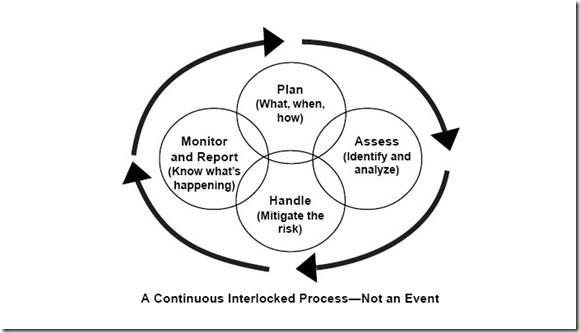
PDCA (ISO/IEC 27001:2005):
- The Plan phase is about designing the ISMS, assessing information security risks and selecting appropriate controls.
- The Do phase involves implementing and operating the controls.
- The Check phase objective is to review and evaluate the performance (efficiency and effectiveness) of the ISMS.
- In the Act phase, changes are made where necessary to bring the ISMS back to peak performance.
- information technology security administrators should expect to devote approximately one-third of their time addressing technical aspects. The remaining two-thirds should be spent developing policies and procedures, performing security reviews and analyzing risk, addressing contingency planning and promoting security awareness
- security depends on people more than on technology
- employees are a far greater threat to information security than outsiders
- security is like a chain. It is only as strong as its weakest link
- the degree of security depends on three factors:
- the risk you are willing to take
- the functionality of the system
- the costs you are prepared to pay
- security is not a status or a snapshot, but a running process.
Security administration is a management issue, and not a purely technical issue.
Critical factors of ISMS:
- Confidentiality: Protecting information from unauthorized parties.
- Integrity: Protecting information from modifying from unauthorized users.
- Availability: Making the information available to authorized users.
CIA leads to:
- business continuity
- minimization of damages and losses
- competitive edge
- profitability and cash-flow
- respected organization image
- legal compliance
The development of an ISMS framework entails the following six steps:
- Definition of security policy
- Definition of ISMS scope
- Risk assessment (as part of risk management)
- Risk management
- Selection of appropriate controls
- Statement of applicability